快速查询整理
文件泄漏
.git
.svn
.DS_STOR
vim泄漏 .index.php.swp
常见web文件泄漏:
index.php~
index.phps
www.zip
www.tar.gz
常见危险函数
strcmp:比较函数,数组绕过
extract:从用户可以控制的数组中导出变量时导致变量覆盖
parse_str:函数去变量解析存在带入未初始化的数据,可以进行url编码,变量覆盖漏洞
intval:取整函数绕过,payload:id=1024.1
ereg:%00截断
addslashes:宽字节注入%df吃掉 \
XFF:X-Forwarded-For: client1, proxy1, proxy2
进制比较:16进制转换
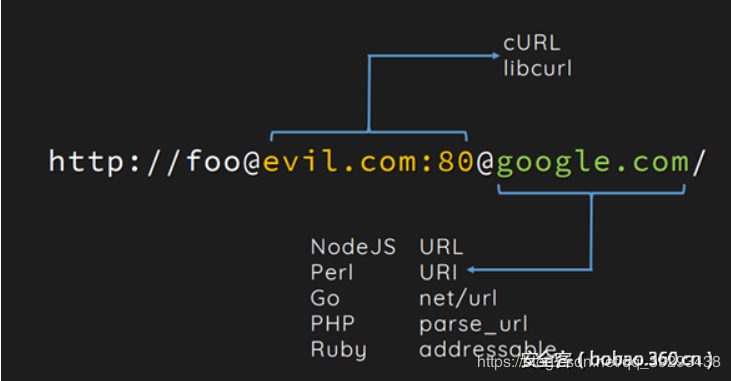
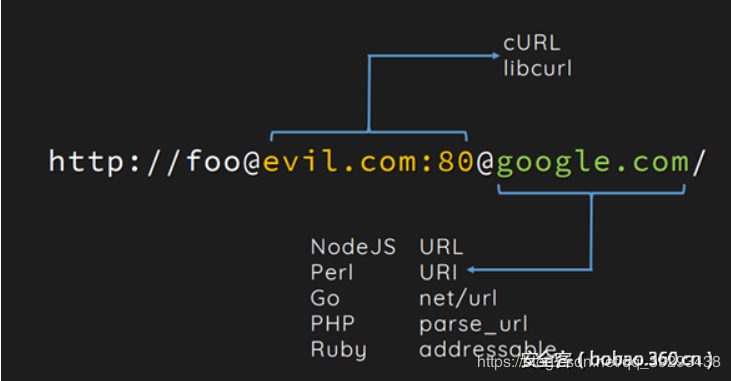
curl与parse_url结合ssrf
文献:https://www.anquanke.com/post/id/86527
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
| <?php
function check_inner_ip($url)
{
$match_result=preg_match('/^(http|https)?:\/\/.*(\/)?.*$/',$url);
if (!$match_result)
{
die('url fomat error1');
}
try
{
$url_parse=parse_url($url);
}
catch(Exception $e)
{
die('url fomat error2');
}
$hostname=$url_parse['host'];
echo $url_parse['host'];
$ip=gethostbyname($hostname);
$int_ip=ip2long($ip);
return ip2long('127.0.0.0')>>24 == $int_ip>>24 || ip2long('10.0.0.0')>>24 == $int_ip>>24 || ip2long('172.16.0.0')>>20 == $int_ip>>20 || ip2long('192.168.0.0')>>16 == $int_ip>>16 || ip2long('0.0.0.0')>>24 == $int_ip>>24;
}
function safe_request_url($url)
{
if (check_inner_ip($url))
{
echo $url.' is inner ip';
}
else
{
$ch = curl_init();
curl_setopt($ch, CURLOPT_URL, $url);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
curl_setopt($ch, CURLOPT_HEADER, 0);
$output = curl_exec($ch);
$result_info = curl_getinfo($ch);
if ($result_info['redirect_url'])
{
safe_request_url($result_info['redirect_url']);
}
curl_close($ch);
var_dump($output);
}
}
$url = $_POST['url'];
if(!empty($url)){
safe_request_url($url);
}
else{
highlight_file(__file__);
}
?>
|
0E开头的两个字符串弱比较:
md5:
QNKCDZO
240610708
s878926199a
s155964671a
s214587387a
s214587387a
sha1:
aaroZmOk
aaK1STfY
aaO8zKZF
aa3OFF9m
常见技巧
php的两个伪协议:
php://input POST原生数据
文件读取file=php://filter/read=convert.base64-encode/resource=index.php
php伪随机数安全:php_mt_seed工具
MISC
明文攻击
crc32爆破
pkcrack参数:
lsb隐写
F5隐写
最低位隐写